9 min read
Overview
Blockchain is not just tech jargon or the magic behind cryptocurrencies but a game-changing technology to keep data trustless, secure, and decentralized.
If you're new to blockchain and want to understand more about blockchain as a technology and would someone need it, check this guide on the basics of blockchain.
How does Blockchains Work?
Think of a blockchain as a shared journal that a group of friends (the participants) decide to keep together. Each friend has their own copy of this journal. Whenever something important happens, like a friend lending money to another, they write it down as a new entry in their journal.
Before an entry is added, all friends must agree that it's true. This is like everyone checking together and saying, "Yes, John did lend $10 to Jane on this date." Once they all agree, they each write down the new entry in their own journals. This way, every friend's journal stays the same, keeping a reliable and tamper-proof record of transactions.
Just like a journal entry can't be erased once it's been written and agreed upon, transactions on the blockchain are permanent and agreed upon by all participants, making it a secure and trustworthy way of keeping records.
Looking at it literally, a blockchain is a network of distributed computers. These computers all store a local copy of the blockchain, which can be thought of as a distributed database or ledger.
Adding data to the blockchain is very similar to our shared journal analogy. When data is added, the change is propagated throughout the network and every computer updates its copy. Every addition or modification is a transaction. All of the transactions that happen within a given timeframe get bundled into a block. Different blockchains have their own mechanisms for determining how long that timeframe is.
This block is then added to the pre-existing chain of blocks, and once this is done, every computer, just like the journal-keeping friends, updates its own copy of the blockchain; that's where the name comes from. It's literally a chain of blocks.
But that's just the beginning of the story. Behind the scenes, a whole array of components and mechanisms are working to keep blockchains secure and operating in a trustless environment. Now, let's dive into some fundamental concepts to get a clearer picture.
Accounts, Transactions, Blocks
In this section, let's understand accounts, transactions, and blocks.
Accounts
Accounts, like in traditional banking or any security scenario, are unique and represent an individual or an entity. Accounts on the blockchain are like unique identities that can be used to send and receive transactions or assets. There are two main types of accounts in smart contract-based blockchains, such as Ethereum. (However, this won't be the case for blockchains like Bitcoin, which do not support smart contracts):
-
Externally Owned Accounts (EOAs): These accounts are controlled by private keys and have no code associated with them. These accounts have token balances and can send & receive transactions, where these transactions can be asset transfer transactions or smart contract interaction transactions. Each account has public and private keypair, where private key is like the password and public key is like an email which is visible to everyone. Example of an EOA on EVM chains,
0x226D82B335C6EE590ba4423f97022a3e71a8f44b -
Contract Accounts: These accounts are owned by smart contracts and can only perform actions or transactions when triggered by an EOA or another smart contract. These types of accounts can hold assets, send transactions, and even execute code when instructions are received in the form of transactions. Example of contract account on EVM chains,
0xdAC17F958D2ee523a2206206994597C13D831ec7
Learn more about Ethereum Accounts.
Transactions
Transactions are the actions initiated by accounts to transfer assets from one account to another, interact with smart contracts, or deploy a smart contract. Every data addition/modification on the blockchain by an account is in the form of a transaction. A transaction in a blockchain typically includes the following information:
-
Nonce: A counter representing the number of transactions sent from an account. Learn about Nonce in this in-depth guide.
-
To: The recipient account address (can be an EOA or contract address).
-
From: The sender's account address (can be an EOA or contract address).
-
Amount: This is the quantity of tokens being transferred (usually the native token of that blockchain).
-
Signature: This is the cryptographic signature generated with the sender's private key. This proves that the transaction was not tampered with and was indeed initiated by the sender's account address.
-
Transaction Hash: This is a unique identifier for the transaction, created by hashing the transaction's details. It's like a fingerprint for the transaction, ensuring its integrity and uniqueness.
Blocks
A block is like a metaphorical package with a list of transactions validated by miners or validators depending on the type of blockchain. These transactions are permanently recorded on the blockchain when included in the block. Some critical components of block information include:
-
Block header: Contains metadata about the block, like the version number, the hash of the previous block (linking it in a chain), the Merkle tree root hash (a cryptographic representation of all transactions in the block), the timestamp, the difficulty target, and the nonce.
-
Transaction List: A list of all transactions included in the block.
-
Block Hash: A unique identifier for the block, generated by hashing the block header through a specific algorithm. It must meet the network's difficulty criteria.
Now, let's dive a little bit deeper into nodes and consensus mechanisms.
Nodes & Consensus Mechanism
Nodes are the computers of the blockchain on which the blockchain network runs, and consensus mechanisms are the rules that govern these nodes' operations.
Consensus Mechanism
A consensus mechanism is like a set of rules or a protocol that allows all the nodes in the blockchain to agree on the validity of transactions and the current state of the blockchain. This ensures that all the copies of the distributed ledger are synchronized and valid. This mechanism is vital for maintaining the decentralized, trustless nature of the blockchain, where all the nodes can agree upon a specific thing without trusting each other. There are several types of consensus mechanisms which has been developed to suit different use cases, but the most common ones are:
-
Proof of Work (PoW): Proof of Work is a consensus mechanism that powers the Bitcoin network. It ensures network security and integrity by requiring miners to solve complex cryptographic puzzles. This process, known as mining, demands significant computational resources, making it difficult for malicious actors to alter the blockchain. The first miner to solve the puzzle validates the transactions and adds a new block, receiving tokens as a reward. PoW's strength lies in its simplicity and proven track record in securing blockchain networks.
-
Proof of Stake (PoS): Proof of Stake represents a shift away from the computational intensity of PoW, focusing instead on choosing a validator algorithmically (depending on the type of blockchain). These validators stake some tokens and are selected to verify the transactions and also block in some blockchains. The algorithm to choose a validator differs from blockchain to blockchain. This mechanism reduces the overall energy consumption of the blockchain network by eliminating the need for mining. PoS democratizes the validation process and aligns the validators' incentives with the network's long-term success, as their stake is at risk if they approve fraudulent transactions.
-
Delegated Proof of Stake (DPoS): Delegated Proof of Stake is an evolution of the PoS mechanism, designed to further increase efficiency and scalability in blockchain networks. In DPoS, token holders vote to elect a small group of validators who are responsible for securing the network and validating transactions. This system allows for more rapid consensus without compromising decentralization, as the elected validators act on behalf of their electors. DPoS also introduces a layer of governance, as validators can be voted out if they fail to perform their duties effectively, ensuring a self-regulating ecosystem.
-
Proof of History (PoH): Unique to Solana, PoH is a high-performance consensus mechanism that enhances scalability and efficiency. It introduces a historical record that proves the time sequence of transactions, allowing for greater throughput without compromising security or decentralization. By incorporating a cryptographic timestamp within each transaction, PoH enables validators to process and validate transactions more swiftly and in parallel, significantly increasing the network's capacity.
Checkout this comprehensive guide on blockchain consensus mechanisms.
Nodes
If we relate to our example from the earlier sections of this guide, nodes are like the journel-keepers who keep track of transactions in their journel. In the context of blockchain, a node is an individual computer participating and connected to the blockchain network. Each node has a copy of the entire blockchain ledger with information about all the transactions ever made on that blockchain network. There are different types of nodes, each serving a specific purpose:
-
Full Nodes: These nodes validate transactions and blocks against the blockchain's consensus rules. If a block or transaction doesn't comply with the rules, it's rejected. Full nodes maintain a complete copy of the blockchain ledger, contributing to the network's security and resilience.
-
Miner Nodes: In blockchain networks that use a Proof of Work (PoW) consensus mechanism, miner nodes compete to solve complex mathematical problems and add new blockchain blocks. The first miner to solve the problem gets to add the new block and is rewarded with tokens.
-
Validator Nodes: In networks utilizing a Proof of Stake (PoS) consensus mechanism, validator nodes validate transactions and create new blocks. Validators are chosen based on the number of coins they hold and are willing to "stake" or lock up as collateral.
-
Lightweight or Light Nodes: These nodes don't hold a complete copy of the blockchain. Instead, they only download the block headers to validate the authenticity of transactions. They rely on full nodes for more detailed transaction data.
Learn more about Ethereum nodes. Now let's go a little bit more technically deep and understand cryptography and hashing.
Cryptography and hashing
Cryptography in blockchain serves as the bedrock for ensuring the security and integrity of data within the network. At its core, blockchain technology leverages cryptographic algorithms to achieve various objectives, including secure transactions, identity verification, and data immutability.
Hashing
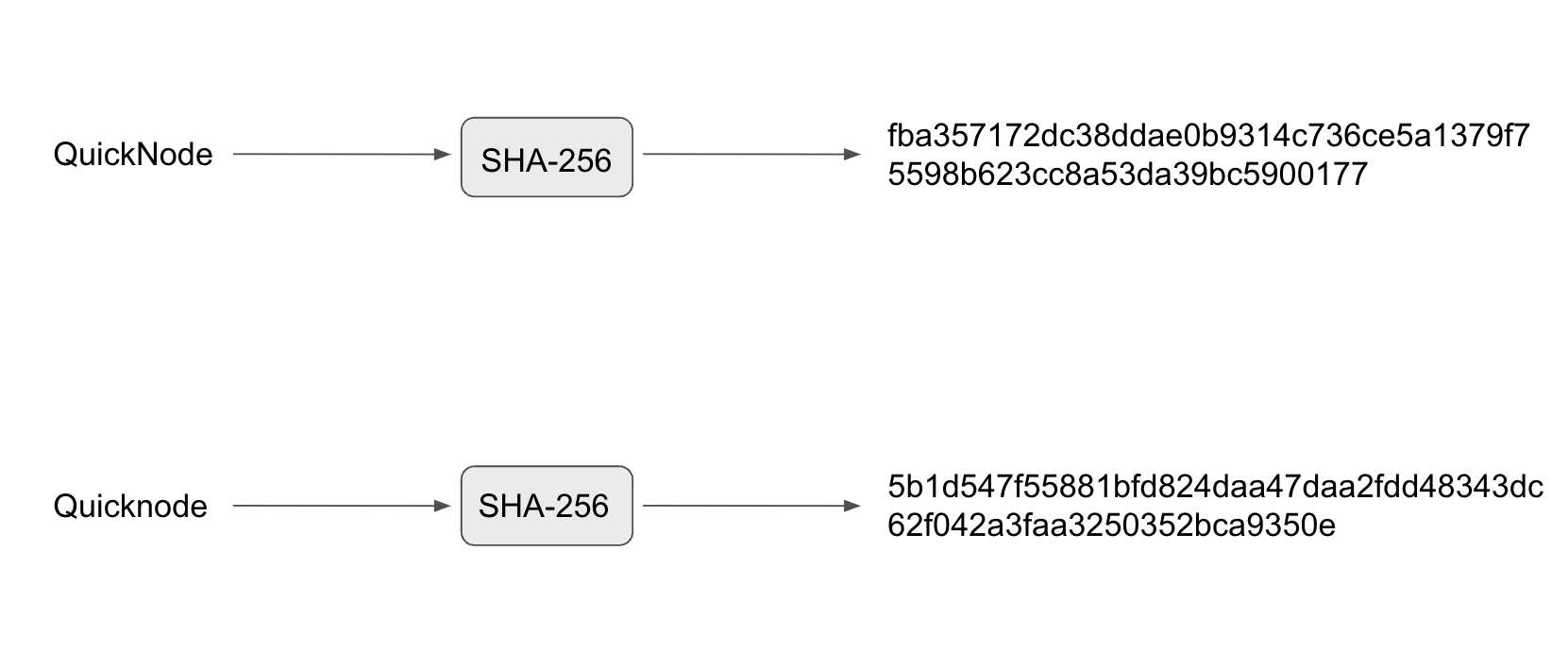
Everything on blockchains is in terms of hashes: transaction identifiers, wallets, block identifiers, etc. The algorithm used to hash particular data differs from blockchain to blockchain, but the requirements and use cases are mostly the same. Each block has a hash of the previous block to ensure a secure chain of blocks resistant to tampering. Hashing also increases the chains' efficiency by processing large amounts of data into a fixed character-length hash string. Due to this, only the hashes need to be compared during any conflicts rather than comparing large amounts of data, which can be slow and resource-intensive.
Key-pair (public-key) cryptography
Blockchains use asymmetric cryptography to facilitate peer-to-peer transactions. Each participant has a pair of cryptographic keys: a public key, which can be shared with others, and a private key, which is kept secret. The account which we saw earlier hold both of these keys. The public key generates a blockchain address, while the private key is used to sign transactions, proving ownership without revealing the private key itself. This mechanism ensures that only the private key owner can authorize transactions from their address.
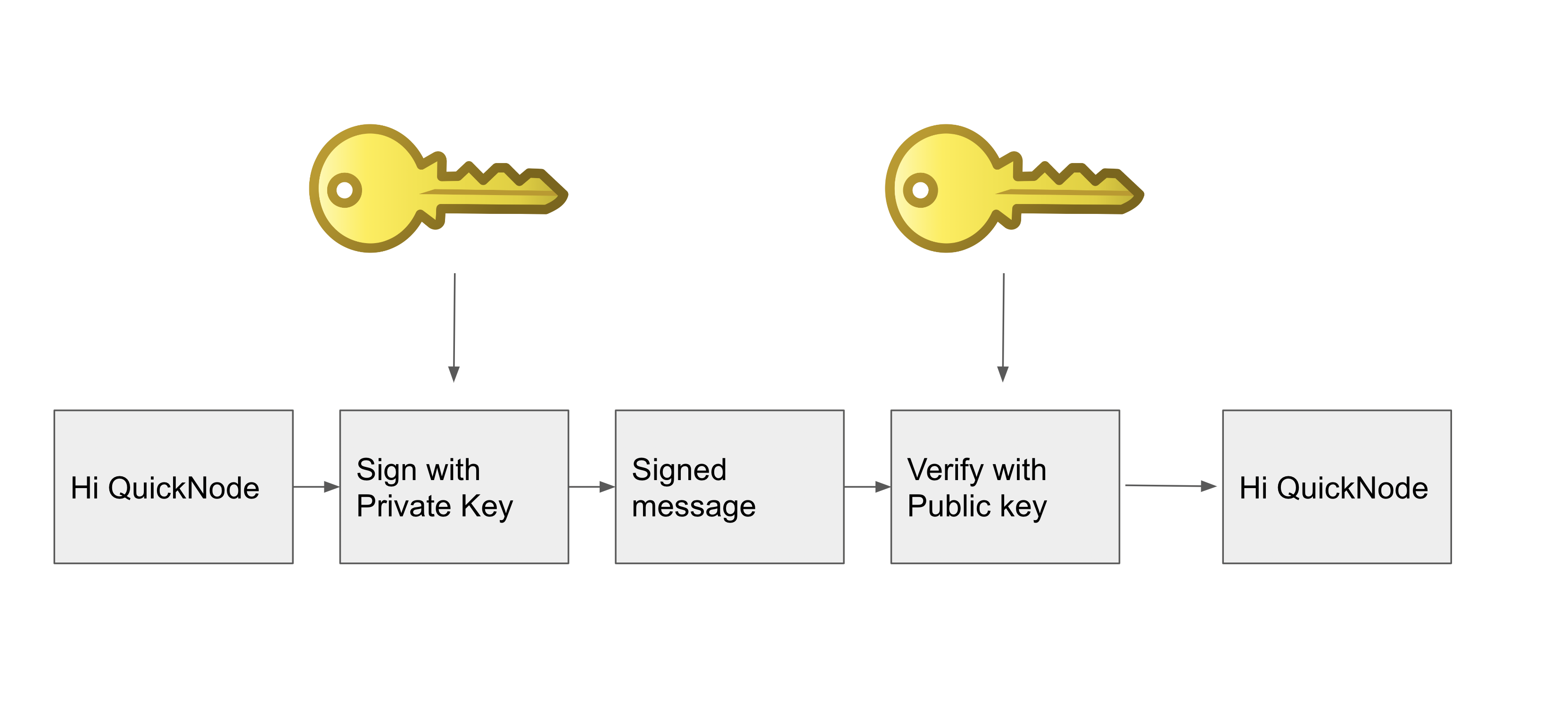
Digital Signatures
Digital signatures are an application of public-key cryptography. When a transaction is made, it is signed with the sender's private key and can be verified by anyone using the sender's public key. This process confirms the transaction's authenticity and integrity, ensuring the sender indeed created it and has not been altered. This also protects against replay attacks, where a third party can try to resubmit the transaction using the signature. However, since the signature is generated using a private key and has other information like a nonce, A transaction with the same signature cannot be resubmitted. Check out how signatures can be verified on Ethereum.
Encryption
While encryption is not used in the blockchain to secure the data (since the ledger is public), it is used during data transmission between network peers to ensure privacy and security. This ensures that sensitive information remains confidential as it moves through the network. A specific output is generated given a particular input; if even a single character changes in the input, the output also changes. This ensures the integrity of data. As you can see in the image below:
Cryptography in blockchain not only secures transactions and data but also underpins the trustless nature of the network. Participants do not need to trust each other, as the cryptographic systems in place ensure that all transactions are secure, verifiable, and immutable. This foundational aspect of blockchain makes it a powerful tool for secure and transparent digital transactions across various applications.
Further Reading
If you made it to this section, you now know a lot about blockchain's inner workings and fundamentals. If you want to learn more about different types of blockchain, then Ethereum and Solana can be a good start.
We ❤️ Feedback!
Let us know if you have any feedback or requests for new topics. We'd love to hear from you.